Ransomware - Scam Email Quoting People’s Postal Addresses -
As per security researcher, an extensively distributed scam email quoting people’s postal addresses tends to link to a dangerous kind of ransomware. After getting to know of an episode of BBC Radio 4’s You and Yours that discuss about the phishing scam, Andrew Brandt, of US firm Blue Coat had got in touch with BBC. He found that the emails seemed to be linked to ransomware known as Maktub.
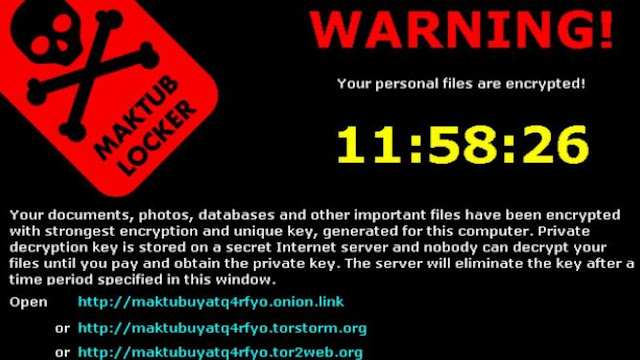
The malware tends to encrypt the files of the victims, demanding a ransom to be paid before they can be unlocked. The recipients were told by the phishing emails that they owed hundreds of pounds to UK businesses and that they could print an invoice by clicking a link. However, according to Mr Brandt that leads to malware. One of the said emails had been received by You and Yours reporter, Shari Vahl. Mr Brandt had informed BBC that `it was incredibly fast and by the time the warning message had appeared on the screen, it had already encrypted everything of value on the hard drive, it happened in seconds’. Maktub does not only demand a ransom but it tends to increase the fee which needs to be paid in bitcoin, as time passes.
Addresses Highly Precise
One of the website connected with the malware had explained that during the first three days, the fee is at 1.4 bitcoins or around $580 and rises to 1.9 bitcoins or $799 after the third day. The recipients are told by the phishing emails that they owe money to British business and charities when they do not owe them anything. One of the organisations named was Koestler Trust, a charity that tends to help ex-offenders and prisoners produce artwork.
Chief executive Sally Taylor told You and Yours that they rely on generous members of the public and was very distressed when they discovered that people felt they had received emails from them asking for money when they had not been generated by them at all. A remarkable feature of the scam was that they included not only the victim’s name but the postal address as well. Several of them including the BBC staff had noticed that the addresses were generally highly precise.
Data Derived from Leaked/Stolen Databases
As per cybersecurity expert at the University of London, Dr Steven Murdoch, it is yet not clear how scammers were able to gather people’s addresses and link them to names and emails. The data could have been derived from a number of leaked or stolen databases for instance making it difficult in tracking down the source.
Many of the people had got in touch with You and Yours team to inform that they were concerned that the data could have been taken from their eBay account since their postal addresses had been stored in the same format there as they seemed to appear in the phishing emails.
The firm had mentioned in a statement that eBay tends to work aggressively in protecting customer data and privacy which is their highest priority and they are not aware of any link between this new phishing scam and the data of eBay. In an effort of creating the safest, environment possible for their customers, they tend to constantly update their approach to customer data security.