WannaCry – Ransomware Programme – Microsoft Windows OS
WannaCry is said to be a ransomware programme affecting Microsoft Windows operating system. A huge cyber-attack utilising it had been launched on May 12, 2017 infecting over 230,000 computers in about 150 countries demanding ransom payments in 28 languages in the cryptocurreny bitcoin. The outbreak spreads by various systems inclusive of phishing emails and on unpatched systems as computer worm which has been defined by Europol as first-time in scale.It was the worst ransomware attack ever faced in the world driving thousands to tears all across the world. WannaCry has held out a blatantwarning regarding the susceptibilities of our digital inter-linked presence. WannaCry is also known as WannaCrypt bug that encodes data on a computer within a few seconds displaying message demanding from the user to pay a ransom of $300 in Bitcoins to restore access to the device together with the data with it.
Most surprisingly the attack also had affected the National Health Service of the United Kingdom obstructing surgeries together with the other critical patients’ treatment all over the British Isles making confidential information and documents of patient inaccessible. Several types of malware affecting a computer are available which may vary from those that may tend to steal your information to those that could delete information which is on the device.
ExternalBlue Exploit
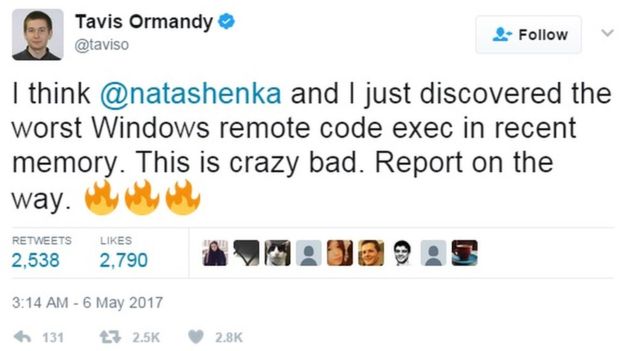
Ransomware as the name indicate foils the user from accessing their devices as well as their data till a definite ransom has been paid to the initiator wherein the computers are locked and encrypts the data on it, thus preventing software together with the apps from functioning. The attack had affected Telefonica together with the other huge companies in Spain together with Britain’s National Health Service NHS, FedEx, Deutsche Bahn and LATAM Airlines.Other targets in around 99 countries had also been reported to have affected around at the same time. WannaCry is said to have utilised the EternalBlue exploit that had been invented by the U.S. National Security Agency – NSA to gain access to Microsoft Windows computers that had been utilised by terrorist outfits and enemy statesin order to affect computers running Microsoft Windows operating systems.
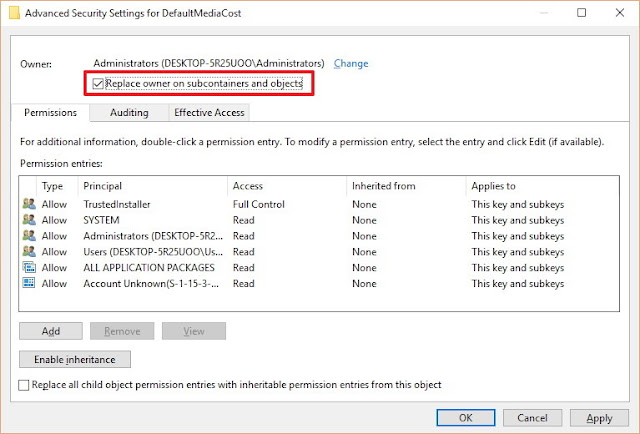
EternalBlue tends to exploit vulnerability MS17-010 in in implementation of the Server Message Block – SMB protocol of Microsoft. Although a patch to eliminate the underlying susceptibility for the supporting systems, - Windows Vista and later operating systems, had been issued on 14th March 2017, delay in apply security updates together with the absence of support by Microsoft of legacy varieties of Windows had left several users helpless.
Under Control – Malware Tech
Owing to the measure of the attack and dealing with the unsupported Windows system together with an effort of controlling the spread of the ransomware, Microsoft had taken the unusual step of releasing the updates for all the earlier unsupported operating systems from Windows XP onwards.The attack had been brought under control by a security researcher, an accidental hero who has asked to be identified only as a MalwareTech. He has discovered a hard-coded security control in the form of a connection to a ridiculous domain name and had bought the domain name for $10.69. This had triggered thousands of pings from attacked devices and killed the ransomware together with its spread.
Had this not been surfaced, there would have been millions of computers all over the world supposedly locked within a few days thus disturbing in all types of global services. Several surgeries had been reported to have been postponed, x-rays were cancels and ambulances had been called back within hours of the attack in the UK where a minimum of 40 hospitals under NHS had been affected.
Shadow Broker
Fear of this type of an attacked had been speculated for a long time which would bring public utilities or transport system to a stop compelling the government to pay a huge amount to bring the service back to normal. This had occurred though for a few hours on Friday 12th May. Interestingly a group known as Shadow Broker had stolen the NSA tool in April who had been unhappy with Donald Trump, the US President whom they had voted for. Microsoft had claimed that it had released a security update addressing the susceptibility which these attacks had exploited in March and had advised users to update their system to deploy latest patches.But in India, regular updates were not done since most of the official computers tend to run Windows and hence the exposure could be great. Personal online data have now been linked to Aadhaar data of more than a billion India.
Regional Director, ComTIA India, Pradipto Chakrabarty had mentioned that the linking of Aadhaar to bank accounts, income-tax together with other personal information has given rise to threat. Since the bank account of the user is connected with his Aadhaar number, the ransomware could probably lock down the account making it inaccessible unless a ransom has been paid.
Common Phishing Tactics
The Head of Asia Pacific, Corporate Business at F-Secure Corporation, Amit Nath had stated that success of the WannaCry ransomware attack has the potential of giving hostile nation state a cause to create cyber weapons where there could be no hope of recovering the data and it could be the worst case scenario.One post accredited to the Principal Security Group Manager, Microsoft Security Response Centre, Phillip Misner had mentioned that the attacks had been utilising common phishing tactics such as malicious attachments asking users to be cautious while opening attachments and the least one could do is to refrain from clicking links which cannot be trusted and stop downloading software from the unfamiliar sources.
F-Secure had also emphasized on the need of a four-phase approach to cyber-security – Predict, Prevent, Detect and Respond, wherein you predict by performing an exposure analysis. Prevent by organizing a defensive solution in reducing the attack surface. Respond by defining on how a breach tends to occur and what are the impacts it tends to have on the systems, detect by monitoring infrastructure for any indications of intrusion or any suspicious behaviour.